I’ve been working on a few different projects in what’s left of my spare time. One of them is battling 419 scammers. I’ll post about that some day soon. The other is phishing investigations. Most have no idea what this really looks like. In one of my catcher email accounts I received an email with the following subject line:
“Action Required – ID Verification”
A catcher account is an account that is not used for any other purpose the attracting spammers, phishers and the like. I “seed” the account by posting comments in random but highly visible guest books. The place most likely to be harvested by these types of criminals. Gmail, as a side note, had already labeled this Action Required email as spam.
The body of the message reads like an offical document:
“Dear Wells Fargo customer,
As you may already know, we at Wells Fargo guarantee your online security and partner with you to prevent fraud. Due to the newly introduced Comprehensive Quarterly Updates Program (which is meant to help you against identity theft, monitor your credit and correct any possible errors), we urge you to go through the 2 steps Wells Fargo Account Confirmation process. The operation involves logging in and confirming your identity over a secure connection at:
https://online.wellsfargo.com/signon?SIGNON_XCP=1010”
First thing to notice is the salutation. Companies like Paypal repeat over and over “we will always adress you by name”. So notice that this mail begins “Wells Fargo Customer”. Ironically the first thing this mail talks about is fraud! This disarms victims. What criminal would speak of the crime right away?? The less technically savvy would not see the second give away. The hyperlinks to the words (which I didn’t copy over in the paste above) do not go to wellsfargo.com. They point to numerical IP’s.
“online security” and “prevent fraud” both have links going here:
http://80.168.169.20/.update/www.wellsfargo.com/cgi-bin/onlinebanking/secure/index.php
Without the use of more sophisticated attacks which would hide even these initials signs one notices www.wellsfargo.com IS in the URL. Just not where it counts. This hyperlink would point one to a server located at 80.168.169.20. The server appears to be offline already but a traceroute (program which shows us the path of a packet) gives an approximate location of this server.
17 112 ms 113 ms 112 ms g1-0-t6-br1.router.uk.clara.net [213.161.70.12]
18 112 ms 114 ms 116 ms t6-cr1-ge-6-0.router.uk.clara.net [195.8.86.205]
19 114 ms 114 ms 113 ms gs-cr2-ge-2-2.router.uk.clara.net [195.8.68.253]
20 114 ms 136 ms 115 ms gs-cr1-ge-2-2.router.uk.clara.net [80.168.0.137]
21 113 ms 115 ms 113 ms fe-2-0-gs-ar5.router.uk.clara.net [195.8.86.26]
22 fe-2-0-gs-ar5.router.uk.clara.net [195.8.86.26] reports: Destination net u
nreachable.
The last stop before getting a “server not found” signal as in the United Kingdom. Interesting.
But the server itself IS still up. And it is located in China!
12 19 ms 18 ms 21 ms 12.118.94.10
13 114 ms 116 ms 114 ms p10-0.zur01b04.sunrise.ch [195.141.213.225]
14 114 ms 114 ms 114 ms g5-1.zur01b03.sunrise.ch [193.192.234.197]
15 113 ms 114 ms 114 ms 212.161.164.37
16 155 ms 134 ms 136 ms 62-167-19-21.adslpremium.ch [62.167.19.21]
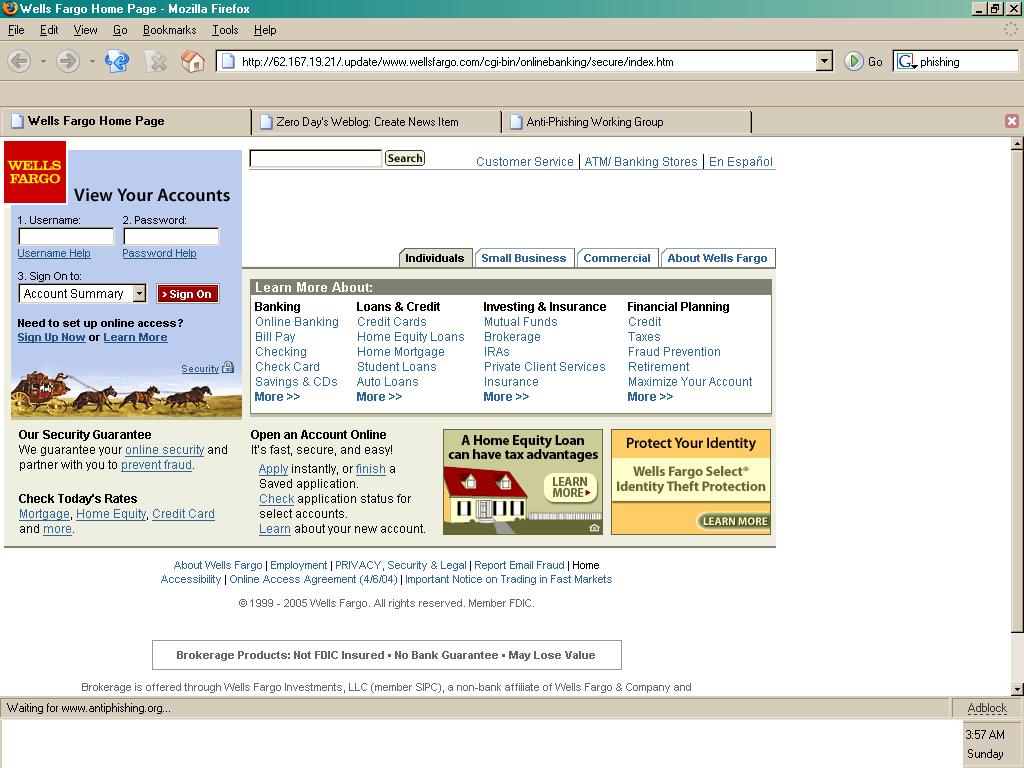
Looking at the site will show an exact replica of the actual Wells Fargo Site. And if you think about it copying and pasting from another web sites design is very simple.
No matter what is entered for the account and password the site goes to the next page. There a pin number is asked for.
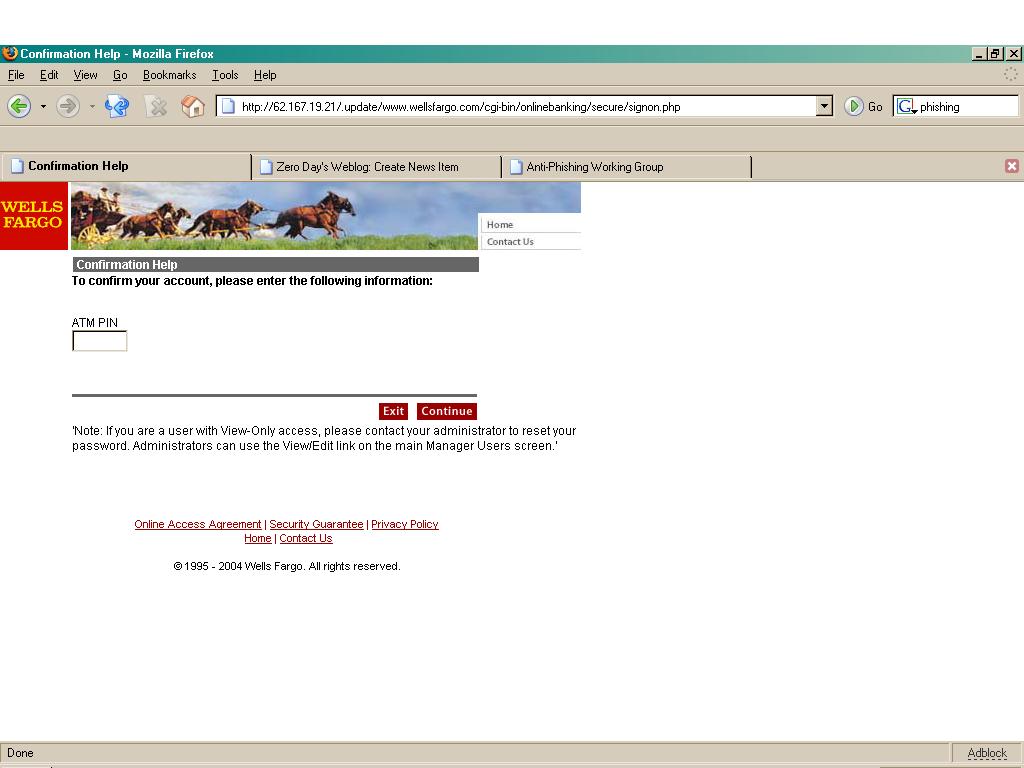
Again any entry is accepted and then, this is clever, a page thanking them for cooperation. The clever part is that all the links go to the actual Wells Fargo site!
This all seems interesting to me at the moment as my paper on Internet jurisdiction looms over me. Suppose you were one of the unfortunate who gave away the information sought. What can one do? Try to contact the police? Interpol? United States Secret Service? The only people that can even possibly help would be the Bank itself. And then they will treat you with indifference if purchases have been made. They have to assume that perhaps you made these purchases on your own and want to get out of paying for them.
As far as jurisdiction prosecuting may be possible for those involved in the UK. We (the US) seem to have good relations with England. Getting someone in China to hand over citizens, even those stealing from the US, will likely get derisive laughter.
Post a Comment