I am pleased to announce the 1.00.00 release of a new templated mega-menu provider. It is based on, and derives its functionality from, the default DNNMenu.
(more…)
Archive for May, 2009
Public Preview: DotNetNuke Templated Mega-Menu Provider
Thursday, May 14th, 2009I am pleased to announce the publically-available preview of a new templated mega-menu provider. This preview is for internal evaluation only, and should not be used in production. A full release, including source, is expected at the end of the month.
The provider allows for marking one or more pages as being templated; during instantiation these templates are dynamically inserted into the page. The templates are highly flexible and may be deployed at the site, skin, or portal level. This allows for great flexibility in user experience.
The project is hosted on CodePlex and is located here.
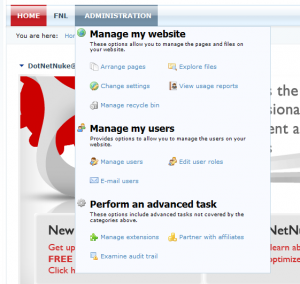
By way of example, the default templates available allows styling of the DotNetNuke administrator menu as:
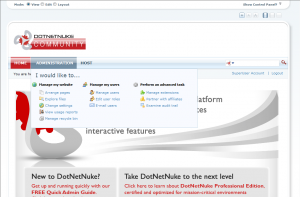
DotNetNuke DNNMenu Templated-Menu Provider Screenshot with Wide Rendering
DotNetNuke Multi-Factor Authentication Provider
Friday, May 1st, 2009I am pleased to announce an initial release of a multi-factor provider for the DotNetNuke content management system.
This authentication provider allows a host to configure enhanced authentication (including SMS, SMTP, YubiKey, and X.509 certificates) for any number and combination of portal roles. Each factor must be fulfilled prior to authentication being granted, increasing overall security.
This package may be downloaded from it’s project site, located at http://dnnmultifactor.codeplex.com.
Goals
- A robust, extensible multi-factor authentication framework for the DotNetNuke content management system.
- Complete integration into the framework using existing extension points, with no core modifications or recompilation required.
- Support for host-, administrator-, and user-level configuration, with the ability to vary required factors across an arbitrary set of roles.
- A robust set of included factor providers, including SMS, secure SMTP, YubiKey (www.yubico.com), and X.509 certificate.
- Extension points in the authentication system allowing for development of custom factors by third parties.
- Reliance on the existing ASP.NET membership subsystem for existing (first-factor) authentication.
- Minimization of “custom security” risk by relying, insofar as is possible, upon existing security infrastructure (ASP.NET membership, DotNetNuke portal security, password generation, et cetera.
- As small an overall surface area as is possible, and an absolute reliance upon the existing ASP.NET membership system as a first-factor fallback, should any unforeseen vulnerability exist.