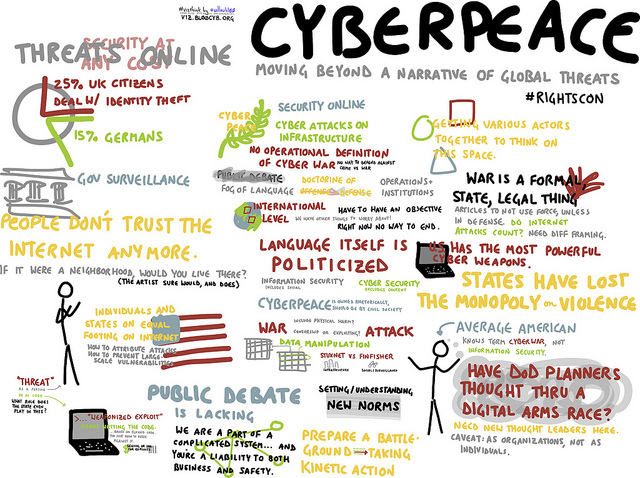
⚐ Cyber Dialogue 2014 – Working group on “Cyber war & international diplomacy issues”
ø
I am just back from the CyberDialogue conference, an event presented by the Canada Centre for Global Security Studies at the Munk School of Global Affairs, University of Toronto, that convenes actors « from government, civil society, academia and private enterprise to participate in a series of facilitated public plenary conversations and working groups around cyberspace security and governance ». The conference was frankly awesome – I’ve always been fan of the Citizen Lab, they deserve major applause for putting together a very productive and unique conference. They did a truly impressive job at convening actors with very different backgrounds and points of view – something that is much needed in that space, as conversations unfortunately tend to happen within echo chambers of like-minded experts.
I was lucky to be among an impressive group of folks for a working group on cyber war and diplomacy. We had a whole day to talk through differences in perspectives, to identify priorities and fault lines and to come up with a short statement of things we could agree on – then point to things we couldn’t reach consensus on.
Below are three points we managed to agree on. It reads a bit mild, because it had to be common grounds and consensual, yet it’s interesting because it stresses the necessity address cyber conflict norms in times of peace.
“1. There exists a need to establish viable norms for state behavior in peacetime regarding cyber security. Much attention has been dedicated to the threshold for cyber action regarding the Law of Armed Conflict, but less about the steady state beneath armed conflict.
2. Attention should be paid to the development of humanitarian principles for cybersecurity. For example, are Computer Emergency/Incident Response Teams (CERTs) off limits for targeting? Can International Committee of the Red Cross principles – neutral, impartial, and independent – be applied to the first responders of cyberspace?
3. International activity on cybersecurity, such as the UN Group of Government Experts on cyber and other multi-national initiatives, should include a mechanisms for inclusionary participation and distributed responsibility beyond government and industry.”
Many thanks to our group moderator, Chris Bronk from Rice University, for compiling these remarks. I am pasting the framing notes of the working group below, along with the conference topic for this year. To keep groups small enough to function, the initial working group topic been separated into “Surveillance and accountability” and “Cyber war and international diplomacy issues”. On one hand, that clearly made us more effective, on the other hand I would have loved to finally see a conversation on how cyberwar institutions and legal frameworks feed into the dynamics of Governmental surveillance. The « domestic » surveillance conversation is often held separately from the « cyberwar » international one, which obscures how deeply they are linked.
More on this later: if more details of the discussion (under Chatham House rules though) are posted, I’ll share links. In the meantime:
⚆ Conference website: http://www.cyberdialogue.ca/2014-agenda/
⚆ 2013 Cyber Dialogue video gives a clear idea of what the conf. feels like: http://vimeo.com/77650794
⚆ Citizen Lab website is filled with great research: http://citizenlab.org/
⚆ Bits of conference wisdom can be found on Twitter hashtag: https://twitter.com/search?q=%23cd2014
⚆ Bonus Twitter feed: https://twitter.com/cyberdiaDoge
✎ WORKING GROUP TOPIC: From Surveillance to Cyber War: What are the Limits and Impacts?
Moderators: Jan Kleijssen (Council of Europe) and Chris Bronk (Rice University)
Description: The Snowden revelations have touched off widespread criticism and alarm of government organized mass surveillance and computer network exploitation and attacks. Yet even liberal democratic governments require well-equipped law enforcement, intelligence, and armed forces to enforce the law and secure themselves from threats abroad. The world can be a nasty place, and we have to live in it. Both mass and targeted surveillance, including computer network exploitation and attacks, are likely going to be a part of the that world for the foreseeable future. What are the proper limits and safeguards of lawful intercept? Do we need new forms of oversight and accountability? How do we reconcile the seemingly conflicting missions of agencies charged to protect domestic critical infrastructure from attack while developing ways to compromise networks abroad? Is there an arms race in cyberspace? How do we control it? Can we develop norms to limit global cyber espionage?
✎ CONFERENCE TOPIC: After Snowden, Whither Internet Freedom?
A recent stream of documents leaked by former NSA contractor Edward Snowden has shed light on an otherwise highly secretive world of cyber surveillance. Among the revelations — which include details on mass domestic intercepts and covert efforts to shape and weaken global encryption standards — perhaps the most important for the future of global cyberspace are those concerning the way the U.S. government compelled the secret cooperation of American telecommunications, Internet, and social media companies with signals intelligence programs.
For American citizens, the NSA story has touched off soul-searching discussions about the legality of mass surveillance programs, whether they violate the Fourth and Fifth Amendments of the U.S. Constitution, and whether proper oversight and accountability exist to protect American citizens’ rights. But for the rest of the world, they lay bare an enormous “homefield advantage” enjoyed by the United States — a function of the fact that AT&T, Verizon, Google, Facebook, Twitter, Yahoo!, and many other brand name giants are headquartered in the United States.
Prior to the Snowden revelations, global governance of cyberspace was already at a breaking point. The vast majority of Internet users — now and into the future — are coming from the world’s global South, from regions like Africa, Asia, Latin America, and the Middle East. Of the six billion mobile phones on the planet, four billion of them are already located in the developing world. Notably, many of the fastest rates of connectivity to cyberspace are among the world’s most fragile states and/or autocratic regimes, or in countries where religion plays a major role in public life. Meanwhile, countries like Russia, China, Saudi Arabia, Indonesia, India, and others have been pushing for greater sovereign controls in cyberspace. While a US-led alliance of countries, known as the Freedom Online Coalition, was able to resist these pressures at the Dubai ITU summit and other forums like it, the Snowden revelations will certainly call into question the sincerity of this coalition. Already some world leaders, such as Brazil’s President Rousseff, have argued for a reordering of governance of global cyberspace away from U.S. controls.
For the fourth annual Cyber Dialogue, we are inviting a selected group of participants to address the question, “After Snowden, Whither Internet Freedom?” What are the likely reactions to the Snowden revelations going to be among countries of the global South? How will the Freedom Online Coalition respond? What is the future of the “multi-stakeholder” model of Internet governance? Does the “Internet Freedom” agenda still carry any legitimacy? What do we know about “other NSA’s” out there? What are the likely implications for rights, security, and openness in cyberspace of post-Snowden nationalization efforts, like those of Brazil’s?
As in previous Cyber Dialogues, participants will be drawn from a cross-section of government (including law enforcement, defence, and intelligence), the private sector, and civil society. In order to canvass worldwide reaction to the Snowden revelations, this year’s Cyber Dialogue will include an emphasis on thought leaders from the global South, including Africa, Asia, Latin America, and the Middle East.







 Share
Share Email
Email Print
Print